TAC, a cross-chain protocol that marketed itself as a bridge between TON and Ethereum, has now reclassified its $2.8 million exploit from May 12 as a white hat event, after the hacker apparently accepted the team’s offer to keep 10% of the “moved” funds in exchange for returning the rest to its multi-signature wallets.
according to TAC Disclosures After the event, the exploit targeted the TON side of the cross-chain layer, resulting in funds being drained across USDT, BLUM, and tsTON. TAC said the vulnerability was isolated to the original TON Jettons that were linked from the TON network, and that the TAC token itself, TON, and all ERC-20 tokens were not affected.
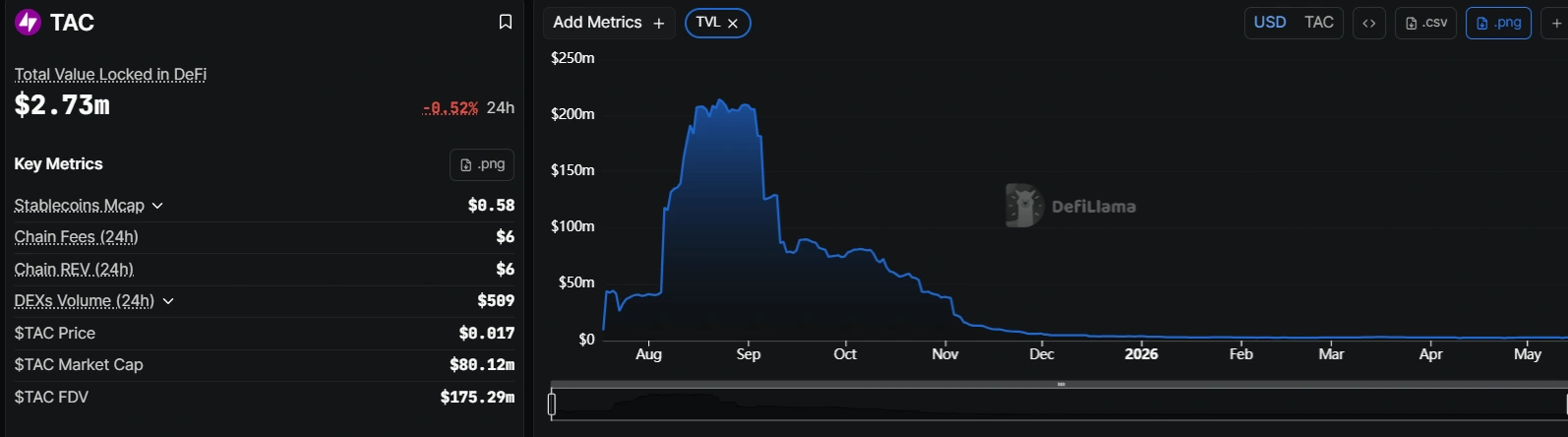
the TAC code It has taken a hit since the exploit occurred, with the price down more than 21% over the past week. The market cap fell to $79 million from more than $91 million before the hack was disclosed on May 12.

TAC’s total worth is approximately $2.74 million as of May 14. For DevillamaWhich means the $2.8 million exploit is roughly equivalent to the protocol’s total TVL value.
How did the TAC protocol exploit occur?
TAC first revealed that it had been hacked on May 12. Message from the team On X It claimed that it temporarily stopped the bridge after receiving reports from its security partners. The team quickly moved to allay concerns by insisting that the issue was limited in scope, affecting only a subset of pooled assets rather than the broader protocol infrastructure.
As for how it will handle the coming days, the TAC Protocol team said: “Our focus is on making users whole and restoring the liquidity of the entire bridge through a legally regulated sale of the institution’s TAC token treasury reserves.”
By May 14, TAC had Positive news To share. The team said that after the exploiter accepted its offer to return the funds to a dedicated multisig wallet on Ethereum and the corresponding address on TON, it reached the decision not to pursue litigation, a decision it coordinated with its security partners and law enforcement.
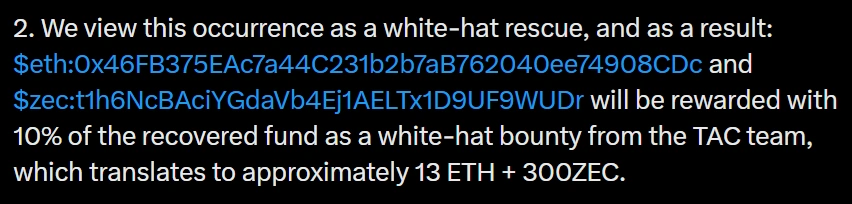
With the refunds, the TAC protocol hack quickly went from exploit to white hat incident, with a 10% reward offered as an incentive, which amounts to about 13 ETH + 300ZEC.
It is standard practice at Web3 to offer hackers a percentage of the stolen funds in exchange for returning the majority of the stolen items. Transit Finance took a page out of that book earlier this week after losing $1.88 million from a discarded TRON smart contract. The team sent an on-chain message to the attacker offering a percentage of the stolen funds as a vulnerability reward for cooperation, with a 48-hour response window.
Hackers pull cross-chain protocols through the wringer
The TAC exploit adds to a pattern of bridge and cross-chain vulnerabilities in early May 2026. Transit Finance attributed its breach to a contract that had been deprecated since 2022 but still maintained exploitable code. Security firm GoPlus Security reported two major private breaches on May 12 totaling $238,000, and blockchain security firm Blockaid identified a $456,000 exploit in Aurelion Labs’ unconfigured Diamond proxy contract on Arbitrum, according to Cryptopolitan Reports.
The losses come on the heels of a rough April. certec I mentioned Nearly $651 million was lost to exploits across the sector that month, the highest level since March 2022, when excluding the Bybit incident in February 2025. The KelpDAO bridge exploit ($293 million) and the Drift Protocol hack ($285 million) were responsible for most of the damage in April.
The individual incidents that occurred in May are smaller by comparison, but their frequency suggests that the underlying conditions that enabled April’s record losses have not been addressed.
The TAC protocol bridge remains paused. The team did not reveal a timeline for resuming operations, but said it would direct the remaining balance, minus the white hat reward, to its multi-signature wallets.