Drift Protocol revealed details about its exploit on April 1, 2026, outlining a coordinated attack built over six months. The decentralized exchange said the hack came after in-person meetings, technical sharing, and the distribution of malware. The incident, which occurred on April 1, involved hacked shareholders and resulted in losses estimated at $280 million.
Drift Protocol tracks long-term social engineering
in X articleDrift Protocol said the attack began around October 2025 at a major cryptocurrency conference. According to the Drift Protocol, individuals posing as a quantitative trading company approached shareholders seeking integration.
However, the interaction did not stop there. The group continued to engage stakeholders across several global industry conferences over a six-month period. They provide verified professional backgrounds and demonstrate technical fluency during frequent in-person meetings.
They also formed a Telegram group after the initial contact. Over time, they discussed trading strategies and potential treasury integrations with shareholders. These discussions followed standard setup patterns for trading companies interacting with Drift Protocol.
From December 2025 until January 2026, the group boarded the ecosystem vault. They provided details of the strategy and deposited over $1 million into the protocol. At the same time, they conducted working sessions and asked detailed questions about the product.
Compromise associated with shared tools and access to devices
As integration talks progressed in February and March 2026, trust deepened. Shareholders met the group again at industry events, strengthening existing relationships. However, Drift Protocol later identified these interactions as a potential stealth vector.
According to Drift Protocol, the attackers shared malicious repositories and applications during the collaboration. This is a complete contradiction ZachXBT callout on the circuit Over $280 million worth of exploitation delays. One contributor reportedly cloned the provided code repository as a front-end deployment tool.
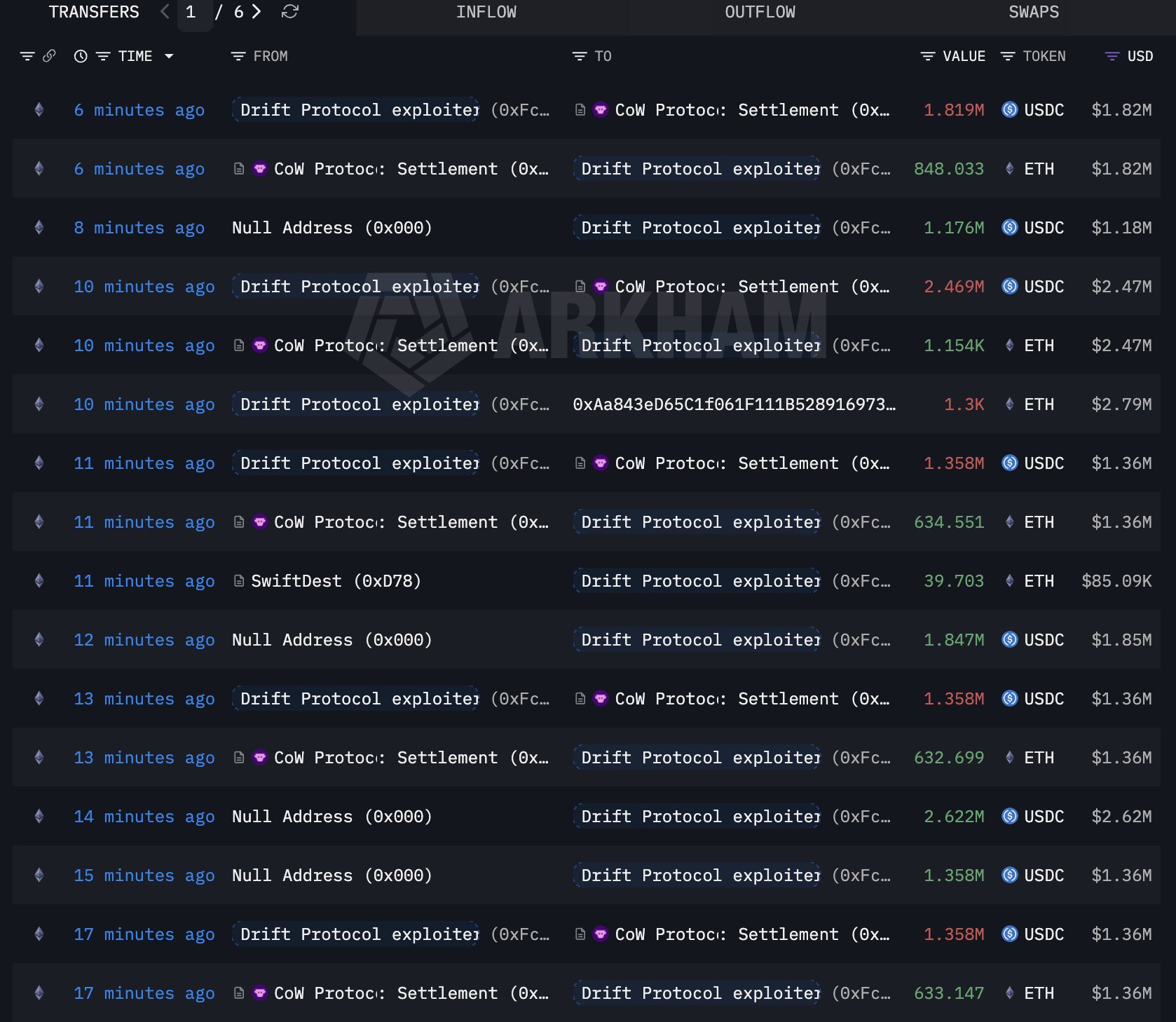
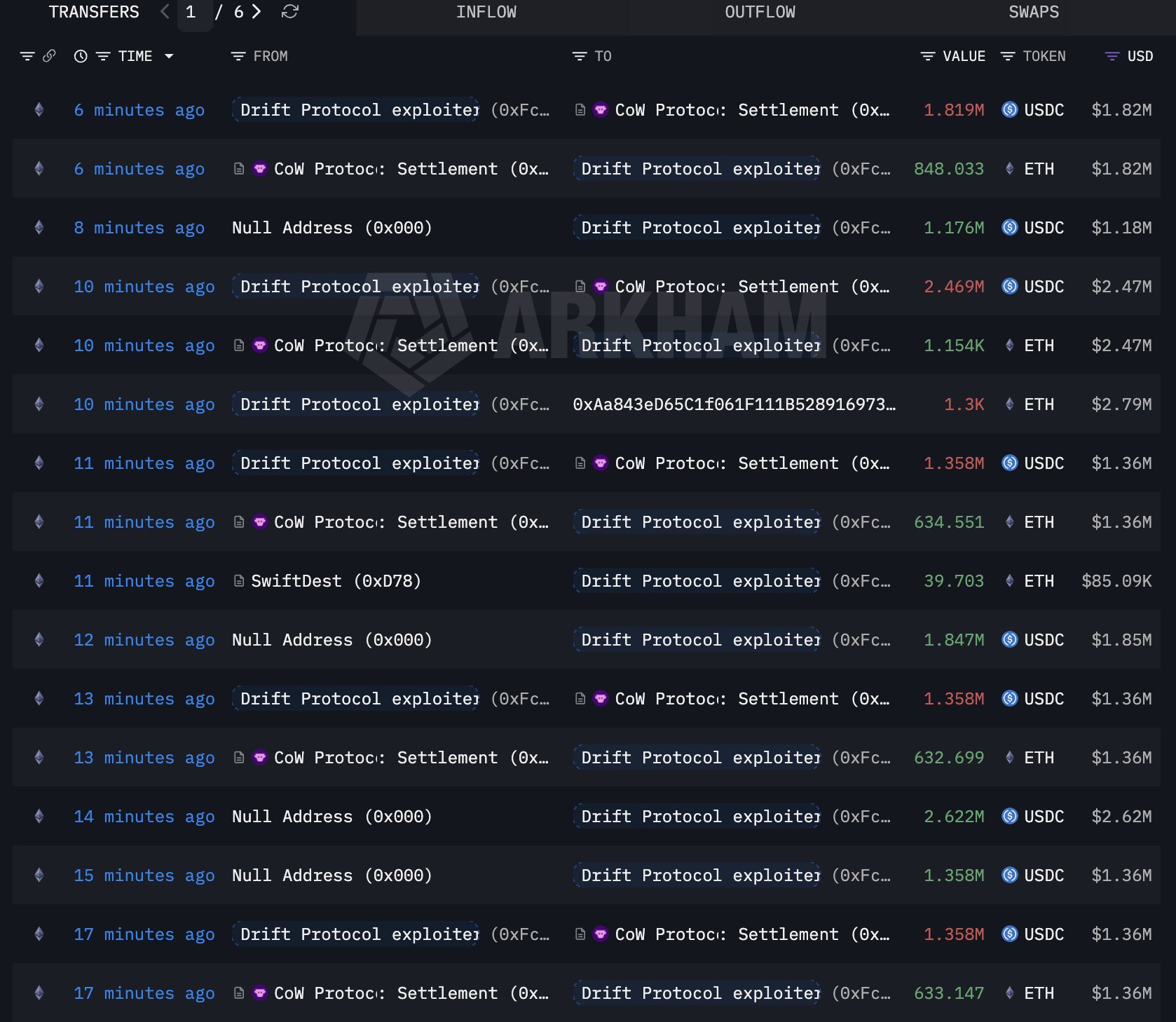 Source: Arkham
Source: Arkham
Another contributor downloaded the TestFlight app described as a wallet product. These actions could potentially put the devices at risk. For the repository vector, Drift Protocol pointed out a known vulnerability in VSCode and Cursor.
During the period from December 2025 to February 2026, opening files may result in silent code execution without warnings. Following the exploit, Drift Protocol conducted forensic reviews across affected devices and accounts. It is worth noting that the attacker and malware’s communication channels are scanned immediately after execution.
Support and ongoing investigative efforts
Drift Protocol said it froze all functionality of the protocol after discovering the exploit. It also removed the compromised wallets from its multi-signature structure and the attackers flagged wallets across exchanges and bridges. The company appointed Mandiant to support the investigation. Meanwhile, the SEALs 911 team contributed analysis pointing to a known threat group.
With moderate to high confidence Decentralized exchange The attack linked to the actors behind the Radiant Capital hack in October 2024. This operation was previously attributed to UNC4736, also known as AppleJeus or Citrine Sleet.
The drift protocol made it clear that the individuals participating in the face-to-face meetings are not North Korean citizens. Instead, she noted, such processes often use external intermediaries for personal involvement.
According to ZachXBT, the activity reflects known DPRK-linked cyber operations that are often grouped under the Lazarus umbrella. He explained that “Lazarus” refers to a group of hacking units, while the DPRK refers to the state’s affiliation behind those operations. He noted that such groups use multi-layered identities, intermediaries, and build long-term access before carrying out attacks.
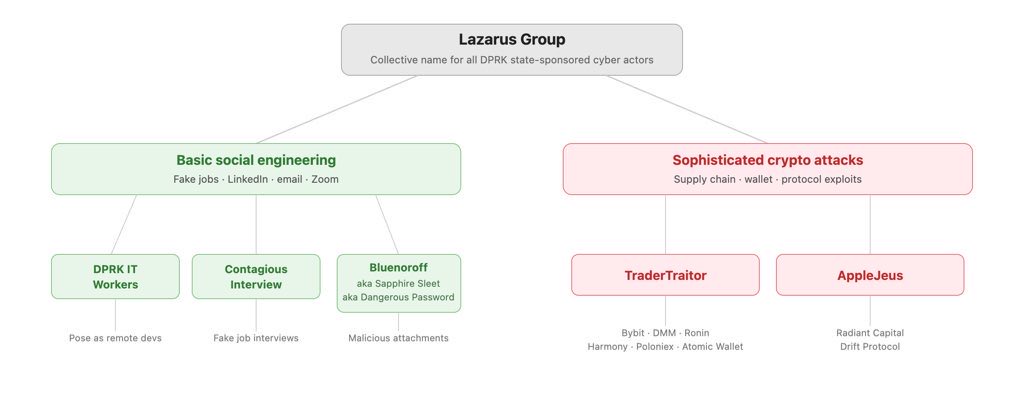
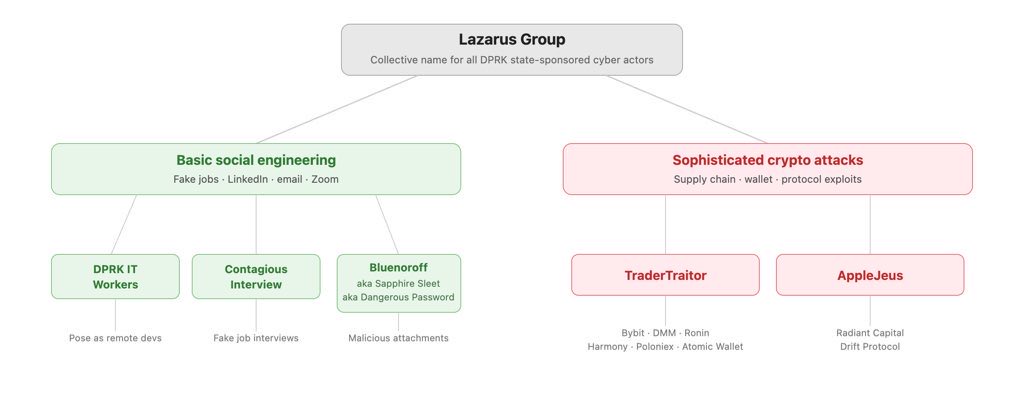 source: ZackXBT
source: ZackXBT
ZachXBT added that on-chain fund flows linked to the exploit show overlap with portfolios linked to previous DPRK-related incidents, including Radiant Capital. He also highlighted operational similarities, including phased interactions, delivery of malware through trusted channels, and rapid cleanup after execution.
Drift Protocol confirmed that all multi-signature signers used cold wallets during the incident. It continues to work with law enforcement and forensic partners to complete the investigation.





