Blockaid recently flagged and red-flagged Aftermath Finance’s perpetual trading system on Sui network It was under active exploitation.
The alert spread like wildfire within the cryptocurrency community, raising alarms that there was a security vulnerability that allowed an attacker to steal large amounts of funds in just minutes.
The analysis shows that $1.1 million USDC was withdrawn from the protocol in 11 rapid transactions within 36 minutes. The attacker exploited a vulnerability in the clearinghouse’s fee accounting mechanism associated with an address.
In the world of decentralized finance (DeFi), if… Capable enough exploitation To take over critical financial operations such as calculating fees and managing collateral, it only takes seconds or minutes for attackers to take advantage.
Fees become profits with Integer Overflow error
At the heart of this vulnerability lies a basic-level integer overflow error, which is a surprisingly common programming error for complex decentralized systems with many interface components.
Graphic values are stored as unsigned 256-bit integers (u256) which can never be negative numbers. What happened is that in one part of the system, these values were misinterpreted as signed integers (which can have both positive and negative values).
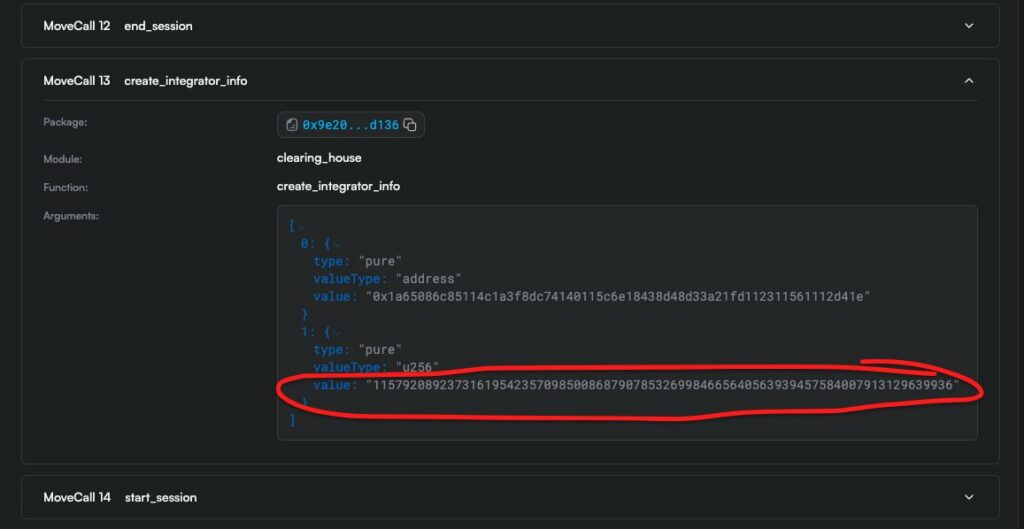
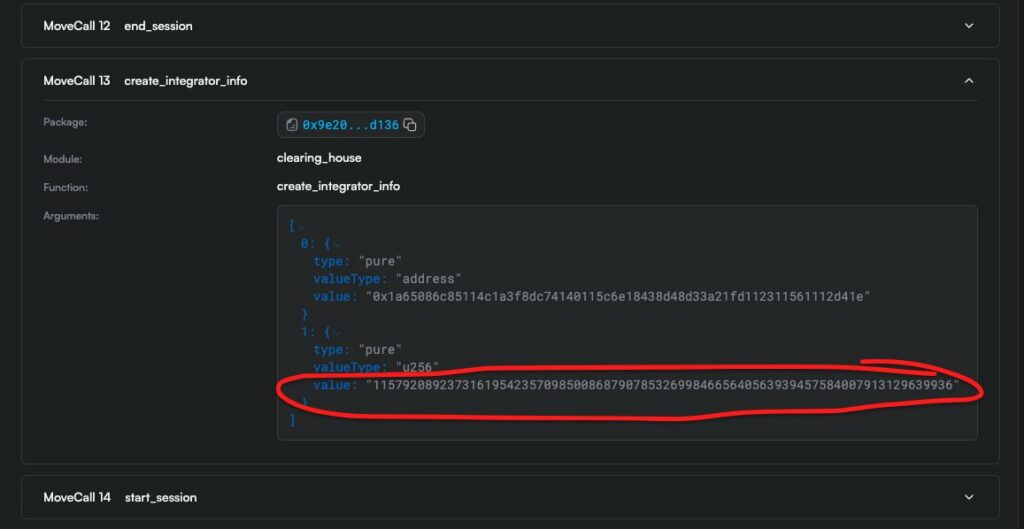
They used this to get around by sending a number just below the top of the u256. As a signed integer, it is read to a large negative number. This reversal in the fee structure transformed fees that should have been charged into payments. As a result, the protocol began paying the costs of trade executions to the attacker who was then able to create artificial collateral and immediately withdraw directly from the protocol vault.
On-chain data confirms that there are no validation guarantees
Exploitation mechanisms are well established in blockchain transaction logs. It actually recorded payments for those negative fees and then rewarded the attacker, rather than receiving fees in return.
The system takes inputs in such a way that it does not apply any arbitrary constraints on those input values, and accepts harmful parameters that contradict its assumption about the object.
Lack of robust input validation is one of the fundamental design errors. In such cases, Validate input parameters Being within expected ranges provides a secure system architecture against such exploits.
Extending parameter validation issues
The Aftermath exploit is one of several parameter validation lapses by multiple DeFi protocols that were noted in April.
Recent cases include:
Uniqueness, where Oracle graphics layer 42 was invalid based on supported layers 100, 500, 3000, and 10000.
The root cause in all cases was adjustment functions that were not imposing constraints on what the input values could be, separate from assumptions made elsewhere in the system.
Security researchers note that attackers are now increasingly using AI-powered tools to automatically investigate edge cases and detect boundary conditions missed by human developers, while defenders have begun incorporating similar automated tools into their security audits.
Although exploitation was severe, the ecosystem response was immediate and effective. Aftermath Finance acted immediately to stop the hack and protect users, with the help of Mysten Labs and the Sui Foundation.
It said the protocol would cover the total losses by fully compensating all affected users. This method is an embodiment of the commitment that more DeFi projects are making to protect users and maintain credibility in times of insecurity.
the The team said afterwards She said in an official statement that she believes this should return to normal soon and praised the quick response of Blockaid and partner organizations.
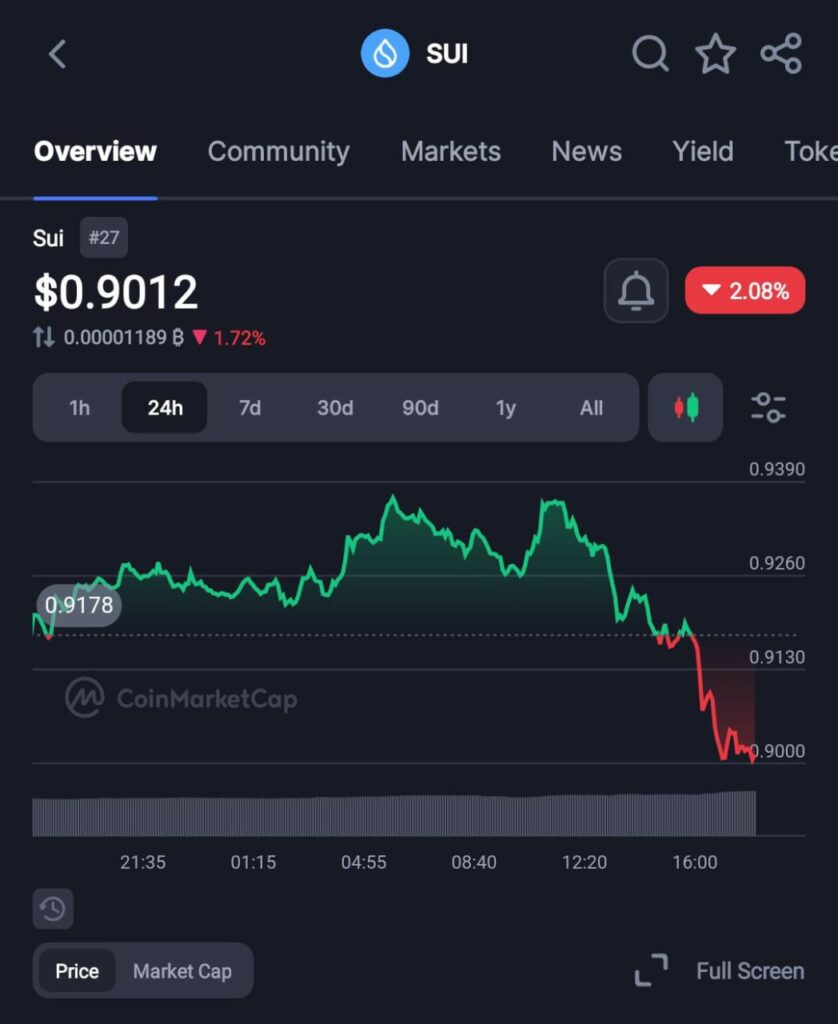
The price is stable, but confidence is shaky
Most importantly, the exploit had little impact on the broader market for Sui tokens. The price of the token has fallen slightly (about – 2%) to $0.90 at the time of writing. This relative stability suggests that market players appear to view the incident as a case of a material failure at the protocol level, rather than a serious, systemic flaw in the Sui network itself.
It also emphasizes the important difference between application-level vulnerabilities and vulnerabilities in the blockchain infrastructure. The aftermath made it clear that the exploit was not due to the Move programming language that powers Sui, but rather due to errors in the protocol implementation.
The Aftermath Finance incident is an unfortunate reminder that broken solutions for protecting decentralized finance systems are far from a solution. Even seemingly benign vulnerabilities (such as integer overflows) in complex smart contract environments can cause serious damage when not researched and managed.
As DeFi grows over time, the need for extensive real-time testing, auditing, and monitoring has become clear. Protocols are designed not only for expected use, but to anticipate adversarial behavior that tests systems to their limits.
AI as a tool for attack and defense represents the beginning of the power of blockchain as an ecosystem. As attackers expand their operations through automation to search for vulnerabilities, developers are coming up with similar techniques to improve audits.
User funds have been secured and recovery is underway at Aftermath Finance, and the immediate crisis now appears to be contained. But we can be certain that the lessons learned from this situation will shape how we approach security and resilience across the industry in a changing and complex landscape.
Disclosure: This is not trading or investment advice. Always do your research before purchasing any cryptocurrency or investing in any services.
Follow us on Twitter @themerklehash To stay up to date on the latest Crypto, NFT, AI, Cybersecurity, and Metaverse news!